Blog
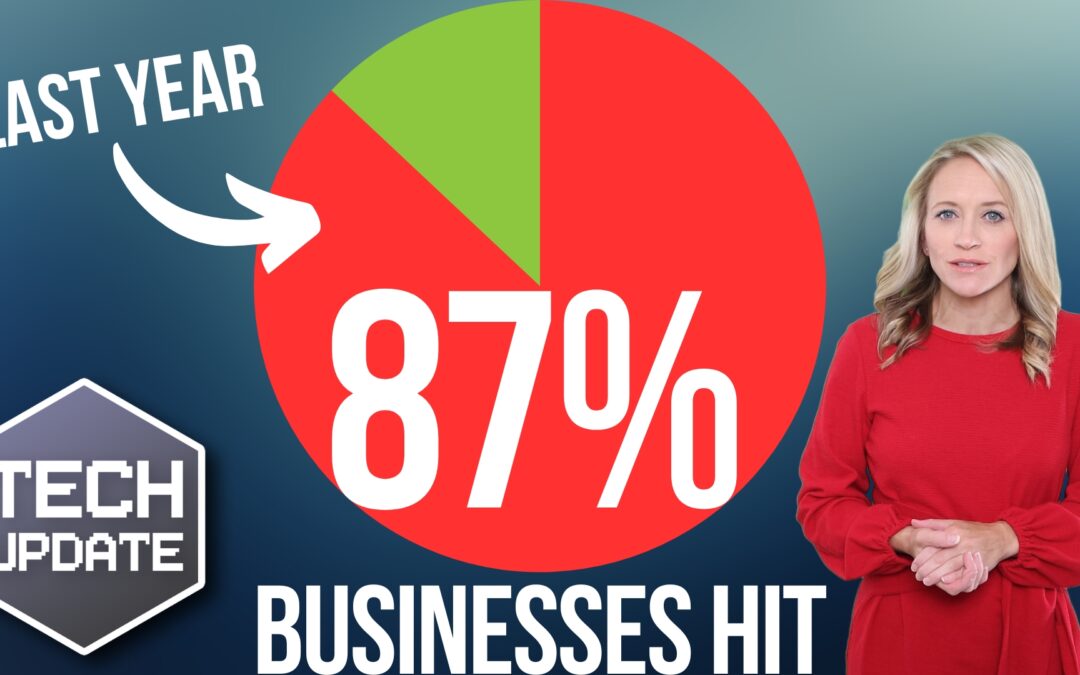
Scary stat: 87% of businesses hit by this in the last year
Cyber attacks aren’t reserved for big corporations. We show you how to protect your business from cyber criminals
Don’t Let These Outsourced IT Myths Limit Your Success
In today’s fast-paced and digitally driven world, the demands placed on the IT infrastructure of businesses like yours are ever-increasing. To meet these challenges head-on, embracing outsourced IT services and entrusting your technological needs to an expert...

This is the latest trend in phishing attacks
Cyber criminals are using images embedded into emails.
We’ll tell you how to protect your business from these new phishing scams.

Privacy alert: Change this setting in Edge, now
There’s a setting in Edge that sends the images you view online to Microsoft. We give you all the details.
What to Look for in an Outsourced IT Partner
In today’s digital age, most businesses rely heavily on technology to streamline their operations and stay ahead of the competition. However, managing an entire IT infrastructure in-house can be overwhelming and costly. That’s where outsourcing IT services comes into...

Browse with confidence: Microsoft Edge’s security boost
We explain how Microsoft Edge is introducing some new security-boosting features to help you stay one step ahead.
Now AI can make your Teams meetings more productive
Microsoft Teams Meeting Recap will summarize your meetings and even make a list of the action points. We show you its other benefits
Stop! And think, before you act on that email
Don’t fall victim to cyber criminals. We explain what a BEC attack is and how to protect your business.
How to Successfully Leverage AI in Your Business
Artificial intelligence (AI) can help organizations like yours gain an edge in today's highly competitive business landscape by increasing efficiency, productivity and profitability. You can improve customer service, enhance marketing efforts, optimize inventory...

Is your business data at risk? Don’t take chances with old tech
Old computers and external drives can put your sensitive business data at risk.
We tell you how to dispose of them in the safest way possible.
How to Stay Ahead of AI-Powered Cybersecurity Risks
While artificial intelligence (AI) has many benefits for businesses, it has also created new vulnerabilities that cybercriminals can exploit to carry out complex cyberattacks that are difficult to detect and mitigate. Using AI, hackers can create convincing phishing...

Here’s how cyber criminals try to hack your accounts while you sleep
Have you ever received a notification on your phone while you’re sleeping, asking if it’s really you logging in?
It’s called a fatigue attack and Microsoft Authenticator’s latest feature will help to protect you.