What Does an IT Due Diligence (DDQ / ODD) Review Look Like for Investment Firms?
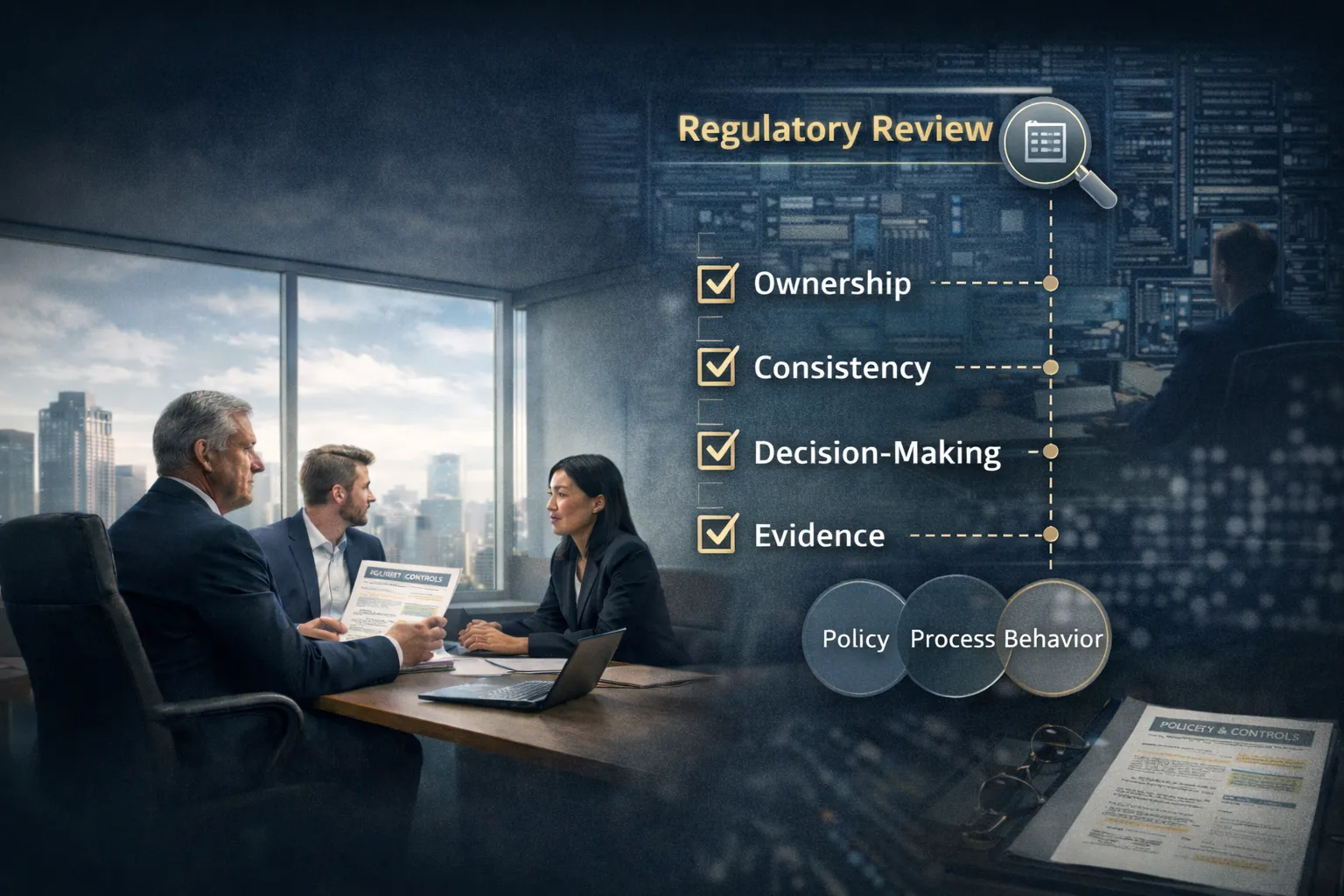
An IT due diligence review for investment firms typically evaluates 25–60 control areas across cybersecurity, infrastructure, data protection, governanc...
Read more about What Does an IT Due Diligence (DDQ / ODD) Review Look Like for Investment Firms?